Little's Law: How to Analyze Your Processes (with Stealth Bombers) | Process Street | Checklist, Workflow and SOP Software

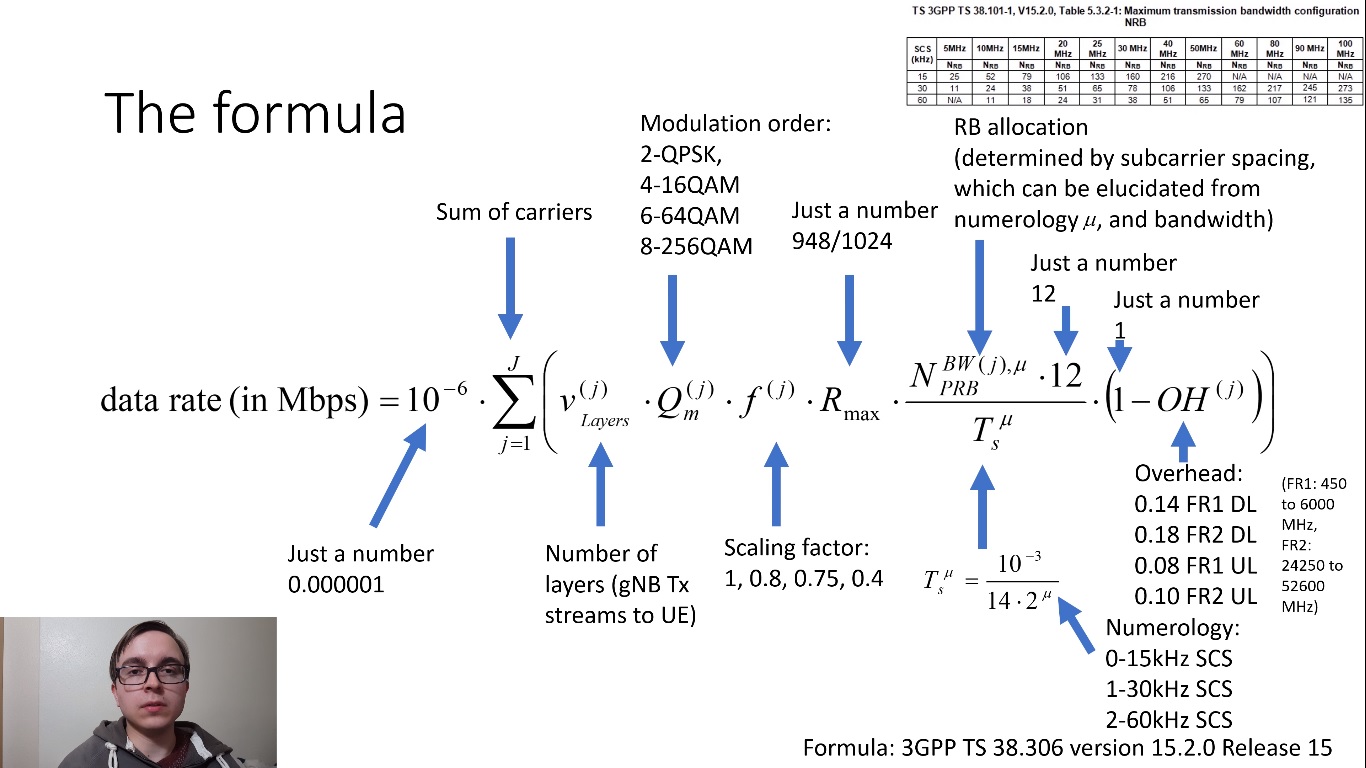
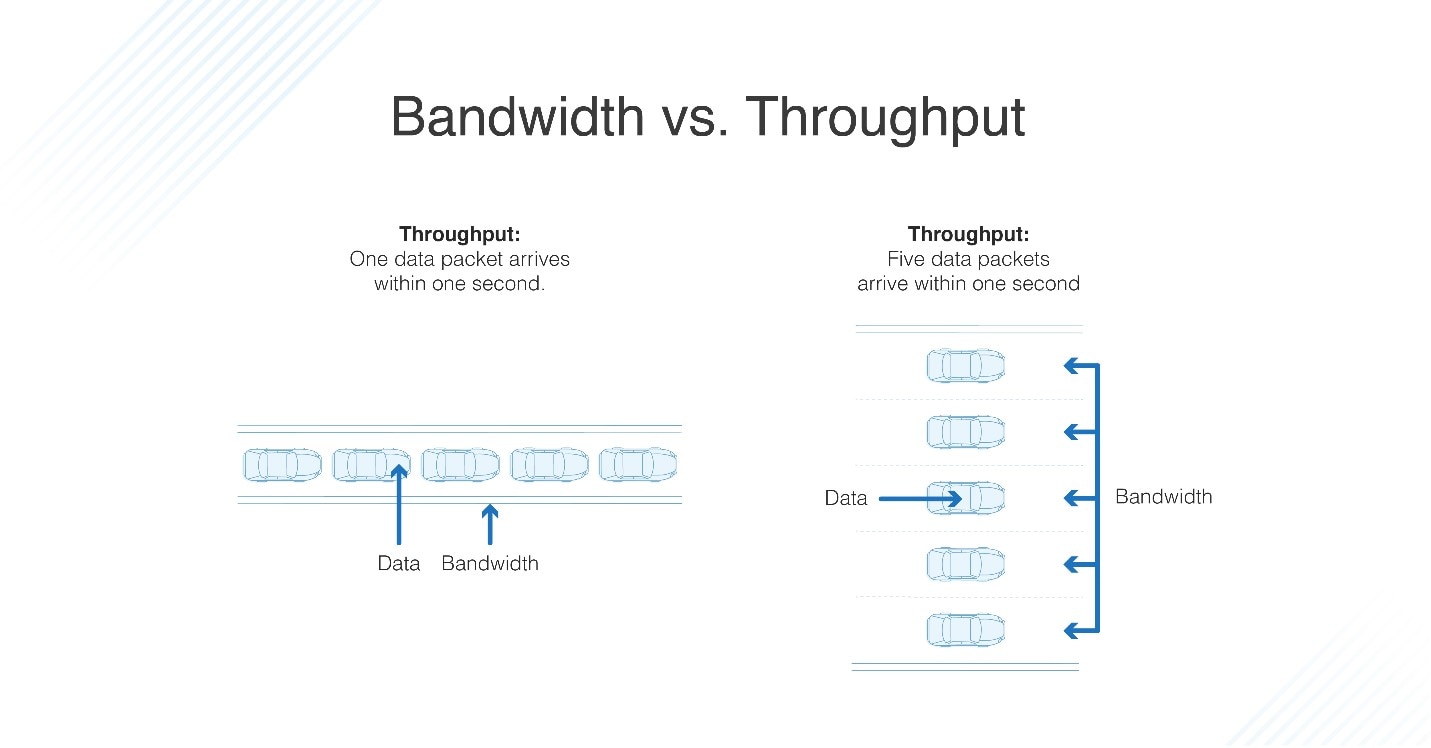
Calculating End-to-End Throughput Capacity in Wireless Networks with Consideration of Hidden Nodes and Multi-Rate Terminals | Semantic Scholar